by Dev Kumar
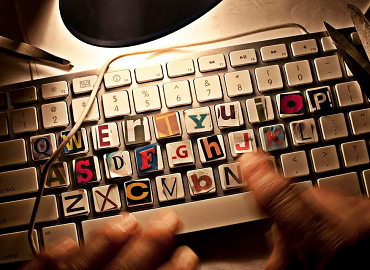
2025 Cybersecurity Trends and Technologies Cybersecurity is crucial for protecting electronic systems and networks from cyberattacks. It encompasses various technological instruments, activities, and techniques to prevent invasion, theft, or destruction. Cybersecurity includes Network Security, Application Security, Information Security, and Operational Security. The Importance of Cybersecurity Cybersecurity is essential for data protection, mitigating third-party regulations, protecting