Cyber Security Threat Types We Circumvent and/or Neutralize
Promotion: Pen Testing Starting $25.00/hr
Attack Solutions, Inc.
A Global Leader In Cyber Security Services
Cyberattacks have grown exponentially over the last few years and since the spread of Covid-19 organizations have experienced a threefold increase in cybercrimes. Attack Solutions, Inc. (ASI) has responded to this increased demand by expanding its human capital of cyber experts, transformed its cyber operational practices, and embraced advance technologies to better confront the security challenges presently inundating organizations. ASI works preemptively with businesses to detect, neutralize, and prevent known threats, and implements robust cyber policies so that businesses are less vulnerable to innovative exploits. We have evolved to become experts at conducting ethical mock attacks against enterprise networks applying some of the most innovative techniques and technologies in penetration testing, network intrusion, and vulnerability exploitation.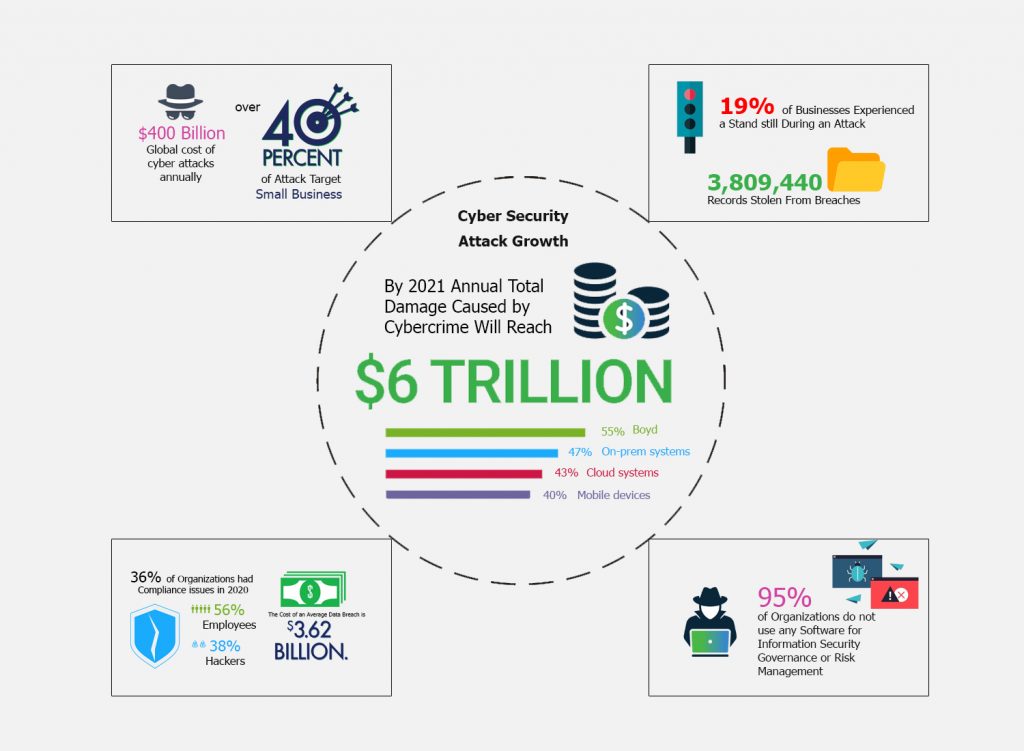 ASI empowers organizations to elevate their security posture through the vigilant execution of ethical mock attacks revealing hidden vulnerabilities and recommending remediation and neutralization approaches. By applying real time analytics, artificial intelligence, and machine learning we baseline global cyber security trends to evolve and adapt potent cyber circumvention remedies to neutralize newer exploit types. Our professional network of global cyber security practitioners and expert ethical hackers become your roster of cyber allies in conducting pen testing cycles, hardening systems, and formulating and implementing robust security policies. ASI has instituted a cyber rapid response team that can be engaged in a moment’s notice to jointly function with your team to circumvent active exploits before penetration and damage can reach an unrecoverable state.
ASI empowers organizations to elevate their security posture through the vigilant execution of ethical mock attacks revealing hidden vulnerabilities and recommending remediation and neutralization approaches. By applying real time analytics, artificial intelligence, and machine learning we baseline global cyber security trends to evolve and adapt potent cyber circumvention remedies to neutralize newer exploit types. Our professional network of global cyber security practitioners and expert ethical hackers become your roster of cyber allies in conducting pen testing cycles, hardening systems, and formulating and implementing robust security policies. ASI has instituted a cyber rapid response team that can be engaged in a moment’s notice to jointly function with your team to circumvent active exploits before penetration and damage can reach an unrecoverable state.Recent Attacks
Cybersecurity researchers have warned of a "resurgence and expansion" of JDY, a covert network associated with China-nexus state-sponsored threat actors. "The JDY botnet comprises over 1,500 SOHO [small office and… [...]
Fortinet, Ivanti, and SAP have released security updates to address multiple critical security vulnerabilities that could result in arbitrary code execution and information disclosure. The security flaw patched by Fortinet… [...]
A high-severity unpatched security flaw in Langflow, an open-source low-code platform to build artificial intelligence (AI) applications, has come under active exploitation in the wild, according to findings from VulnCheck.… [...]
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added three new vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, following reports of active exploitation. The list of vulnerabilities… [...]
Your pentest report looks clean. That might be the problem. Run automated pentesting long enough, and the new findings start to dry up. By the third or fourth run, fewer… [...]
Recent Announcements
MSSQLand enables red teams to interact with MS-SQL servers and linked instances in restricted environments without complex T-SQL queries. Assembly-ready tool for lateral movement. [...]
Credential stuffing drove 22% of all breaches in 2025. How combolists, infostealers and ATO tooling are fuelling enterprise account takeover at scale [...]
DumpBrowserSecrets extracts saved passwords, cookies, OAuth tokens and autofill data from Chrome, Edge, Firefox, Opera and Vivaldi, bypassing App-Bound Encryption via Early Bird APC injection. [...]
Systemic ransomware events in 2025, how Jaguar Land Rover’s shutdown exposed Category 3 supply chain risk, with lessons from Toyota, Nissan and Ferrari. [...]
SmbCrawler is a credentialed SMB share crawler for red teams that discovers misconfigured shares and hunts secrets across Windows networks. [...]

Get a Quote
If you have questions or comments, please use this form to reach us, and you will receive a response within one business day. Your can also call us directly at any of our global offices.