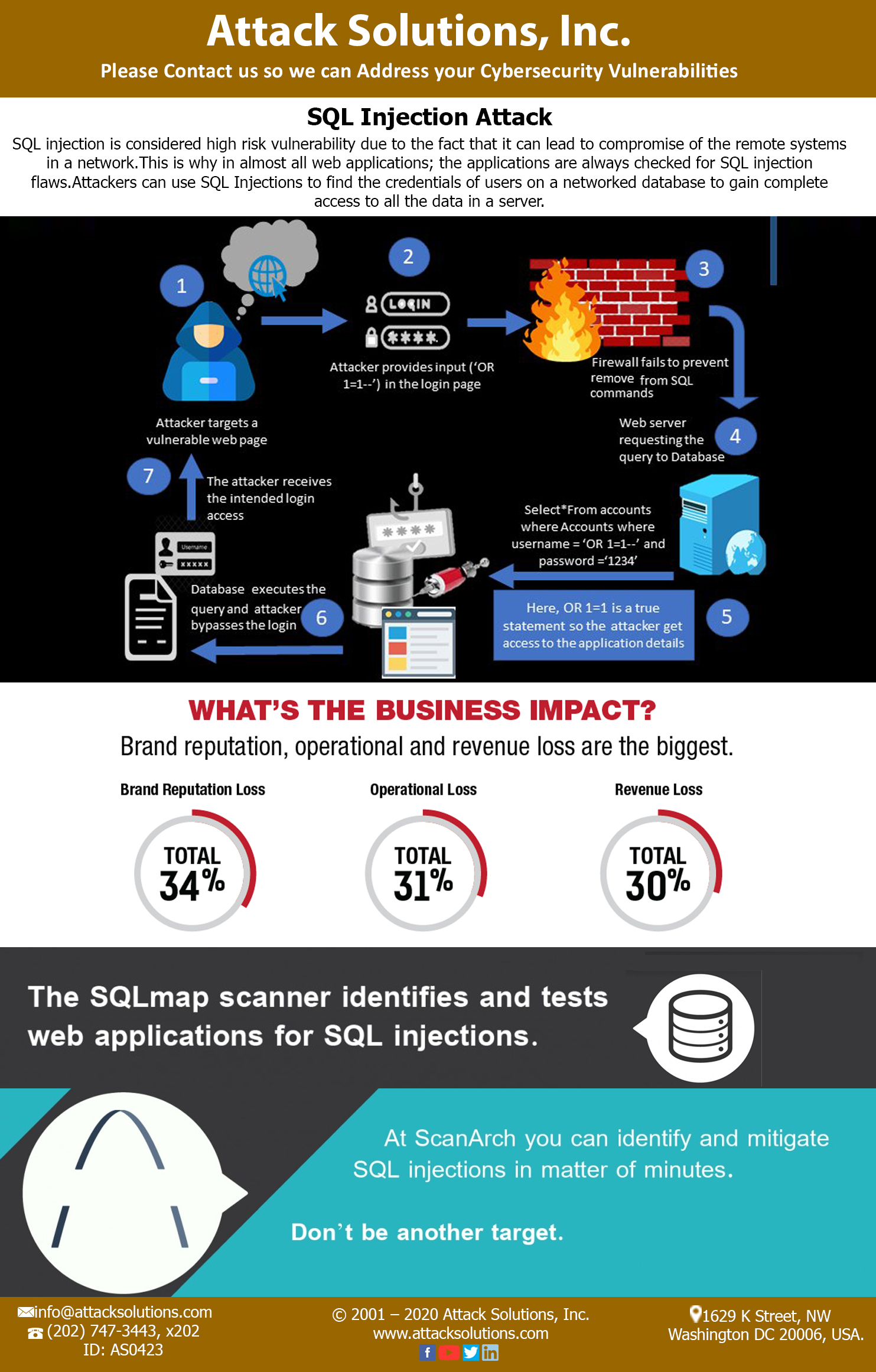
SQL Injection (SQLi) is a form of a database attack in which a hacker exploits database vulnerability of a website to inject malicious code into the SQL query designed to retrieve data. SQLi attacks enable hackers to access sensitive information like usernames, passwords and other personal information stored in the database thus offering complete dominance over a web application. While there are different kinds of SQLi attacks, all forms require the SQL code to be inserted into the preexisting code of the web application. The distinct forms of SQL injection procedure include form and cookie injections and Second Order SQL Injection.
As databases are employed in virtually all web applications, they are particularly vulnerable to SQL injection, thus making SQLi one of the most common forms of attack. The best way to prevent SQLi attacks is to restrict access to database tables. Web applications must not be able to modify, delete or drop tables unless essential. Inputs must be validated, while queries must be well designed to include parameters and user-based input must be restricted, if not avoided completely. Stored procedures in a database make a web application less susceptible to SQLi attacks.
The Attack Solutions Penetration testing team devises a set of queries to identify basic vulnerabilities via unconventional methods that developers do not normally employ. Attack Solutions team also provides a firewall designed to protect users based on an exhaustive list of vulnerabilities and constantly updates security regulations that are set based on parameters like signature recognition, IP reputation, and other security methodologies. The team identifies and blocks SQLi attacks with precision and alerts users and Web administrators regarding possible threats faced by their application.