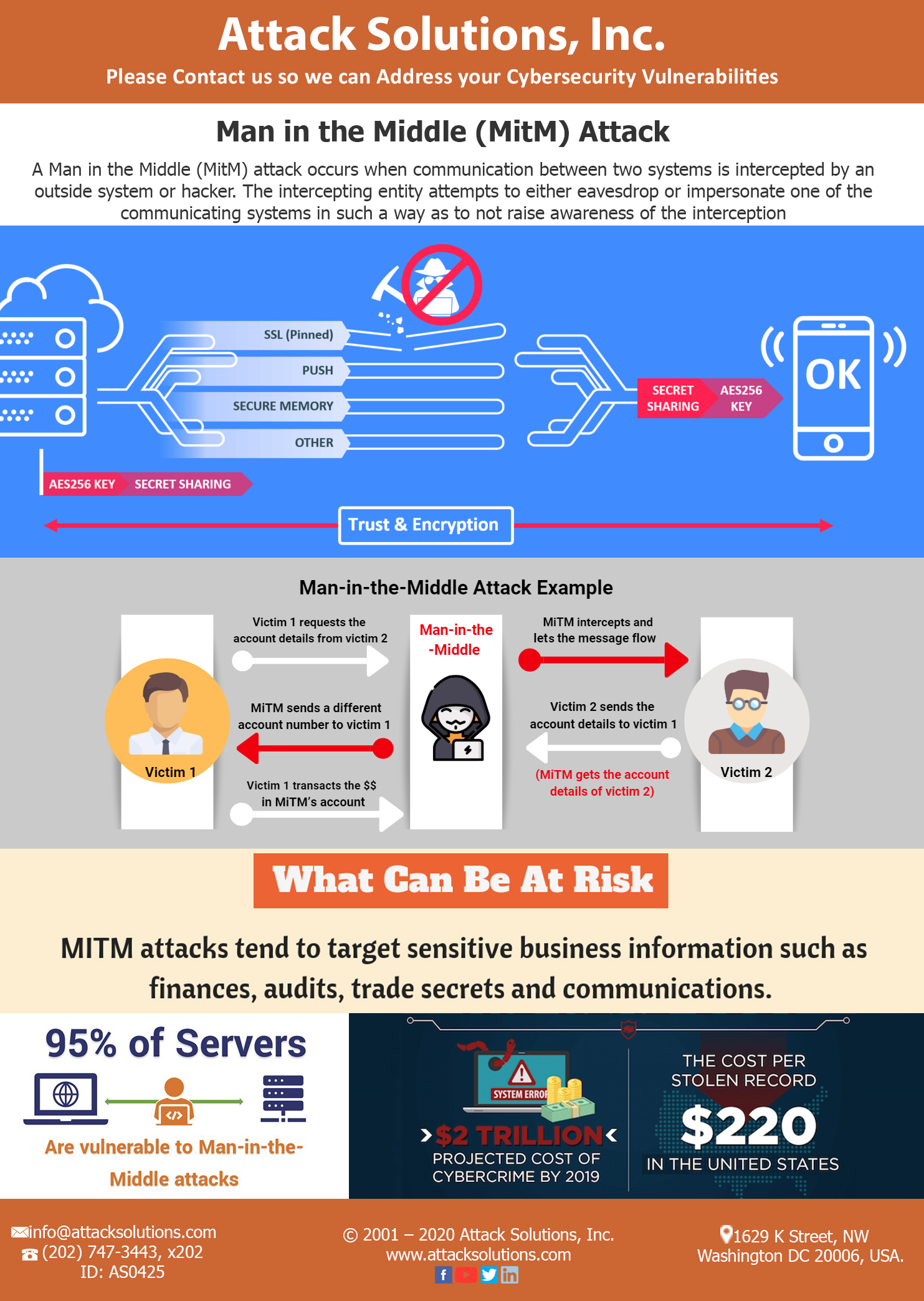
A Man in the middle (MITM) attack enables hackers to intercept communication between two or more parties. A MITM attack requires an access point to “eavesdrop” on a communication between two servers, thus the name, “Man-in-the-middle”. Different types of MITM attacks include Rogue Access Point Attack-attacks perpetrated from rogue WiFi access points, Address Resolution Protocol (ARP) Spoofing-attacks manipulating MAC address resolution, DNS and mDNS spoofing-Altering a website’s address record by infiltrating a DNS server over a Local Area Network (LAN). When IoT devices are connected to the LAN, attackers can easily access and spoof the network to retrieve sensitive information.
Hackers usually execute “Man-in-the-middle” attacks in two steps, interception and decryption. MITM attacks use various techniques like Sniffing- using packet capture tools to inspect low level packets, Packet Injection- injecting malicious packets into the data communication stream between two devices, Session Hijacking – hijacking user sessions by identifying the session token and impersonating a user to send out requests for information and SSL Stripping – intercepting packets to alter their HTTP requests to an equivalent HTTP endpoint, thereby forcing the host to make unencrypted requests to the server, sending out and retrieving sensitive information as simple plain text.
AttackSolution provides strong WEP/WAP encryption at wireless access points thus preventing unauthorized users from accessing the network. The stronger the encryption, the safer the user’s system. We also provide Virtual Private Networks (VPN) that provide a key based encryption to secure all communication packets. Public Key Paid based authentication like RSA can be deployed in multiple layers to ensure legitimacy of devices you are connected to. Besides various forms of protection against MITM attacks, awareness and caution are essential to avoiding such attacks. AttackSolutions offers training material as well as on-site or online training tailored to the customer’s requirement.